Cybersecurity and OSCAL: Geek perspective; ‘C level’ perspective
Member post by: Robert Ashcraft, CMMC Solutions | October 15, 2020
“OSCAL is designed to take disparate control definitions from different sources and express them in a standardized way using its control element.”
“The definitions of controls vary greatly from one standard or guideline to another in terms of the level of detail and the types of information the definitions include. A control definition may be as simple as, “The organization has an access control policy and procedures”, but most are considerably more complicated.”
No matter what framework or frameworks you decide your company should follow, Cybersecurity is the security for the modern age. We have always had security. But with the advent of the WWW, the bad guy has found an open market for their taking. The 21st Century has framed WWW security as “Cybersecurity”.
A company can now achieve security compliance in multiple arenas with a streamlined approach using OSCAL (the Open Security Controls Assessment Language). Executives, Assessors, Policy Authors, and Security Professionals will appreciate the benefits of OSCAL. OSCAL can bring Executives more statistics for global compliance in their vertical. Executives just need to be armed with the knowledge and understanding of what OSCAL can provide their company’s compliance. The Assessor will be able to digest the security information that arises from multiple frameworks. Policy Authors can further define, characterize and customize security controls in policy documents. Security Professionals can document the company’s security controls and how they get applied in critical systems.
Let’s take a look at some examples in which OSCAL and Cybersecurity frameworks can help advance your company.

The ‘C Level” Perspective
Let’s first look at the C Level perspective for OSCAL! Since OSCAL analyzes Cybersecurity Frameworks: NIST 800-53, FISMA, HIPAA, PCI DSS, NIST 800-171/CMMC, CoBit and ISO 27002, C Levels will ask “What is the benefit of the OSCAL Cybersecurity Framework’s comparison?”
Let’s look at a few scenarios:
- I was fortunate to attend an OSCAL workshop last year at which a representative from FedRamp was in attendance as well. The representative stated that they have already started to integrate OSCAL to assist in gaining efficiencies to reduce the time required to be FedRamp certified. The other attendees were also looking to gain efficiencies. Corporations strive to adapt a Cybersecurity framework into their infrastructure. Corporations may be already ISO certified, but see a need to migrate to NIST 800-53 framework. OSCAL will allow the company to take existing discoveries of their current infrastructure, in this case, ISO, in order to reduce the time to develop a NIST 900-53 framework. The OSCAL mappings will bring the data from ISO to NIST 800-53, not only today, but also in the future. The ISO case (company) continues to be ISO certified and assess their ISO controls, but will be able to import the ISO work to NIST 800-53 ongoing.
- A financial company may use CoBit for their framework.They may be looking for a System Security Plan (SSP), where the NIST 800-53 is their preferred methodology. Now, the financial company can use the existing CoBit work to accelerate their SSP development. I have personally been in this situation and believe me, creating a SSP with NIST 800-53 is a full-time job. OSCAL provides an efficient way to cut out double work during the SSP analysis. The financial company now has the option of using the NIST 800-53 SSP (such as the FFIEC) or the OSCAL SSP. Hence, OSCAL streamlines the review and assessment process.
- Next, a look at a tech company, who already uses NIST 800-53. Tech wants to jump into the CMMC world and bid on government (defense) contracts. Since the CMMC readiness is not a low-cost process, Tech looks to utilizing OSCAL’s functionality for cost savings. Tech can use their current NIST 800-53 assessment to ‘Check Off’ many of the CMMC practice assessments that reside in the CMMC/NIST 800-171 format.
The end result of both of these scenarios produces a standardized, ongoing process, of simplifying creation and maintaining the SSP and ease of compiling a new assessment. The OSCAL system security plan model allows data to be analyzed using automated processes along with streamlining the review and assessment process.
Cybersecurity systems and reports will now be more up to date. Flexible data provides usable information in standard formats for management. Thus, relationships drawn between policies, processes and procedures with the component definition model assist the company with their control implementation.
The Geek Perspective
So now let’s be the Geek and look at the OSCAL definition: OSCAL is the Open Security Controls Assessment Language. NIST, in collaboration with industry, has developed and continues to mature the Open Security Controls Assessment Language (OSCAL). OSCAL being a set of formats expressed in XML, JSON, and YAML provides machine-readable representations of control catalogs, control baselines, system security plans, and assessment plans and results.
The Geek or tool developer will be able to build tools and utilities with OSCAL. When using Information in OSCAL Formats the Control-based information expressed using OSCAL formats allows you to:
- Easily access control information from security and privacy control catalogs
- Establish and share machine-readable control baselines
- Maintain and share actionable, up-to-date information about how controls are implemented in your systems
- Automate the monitoring and assessment of your system control implementation effectiveness
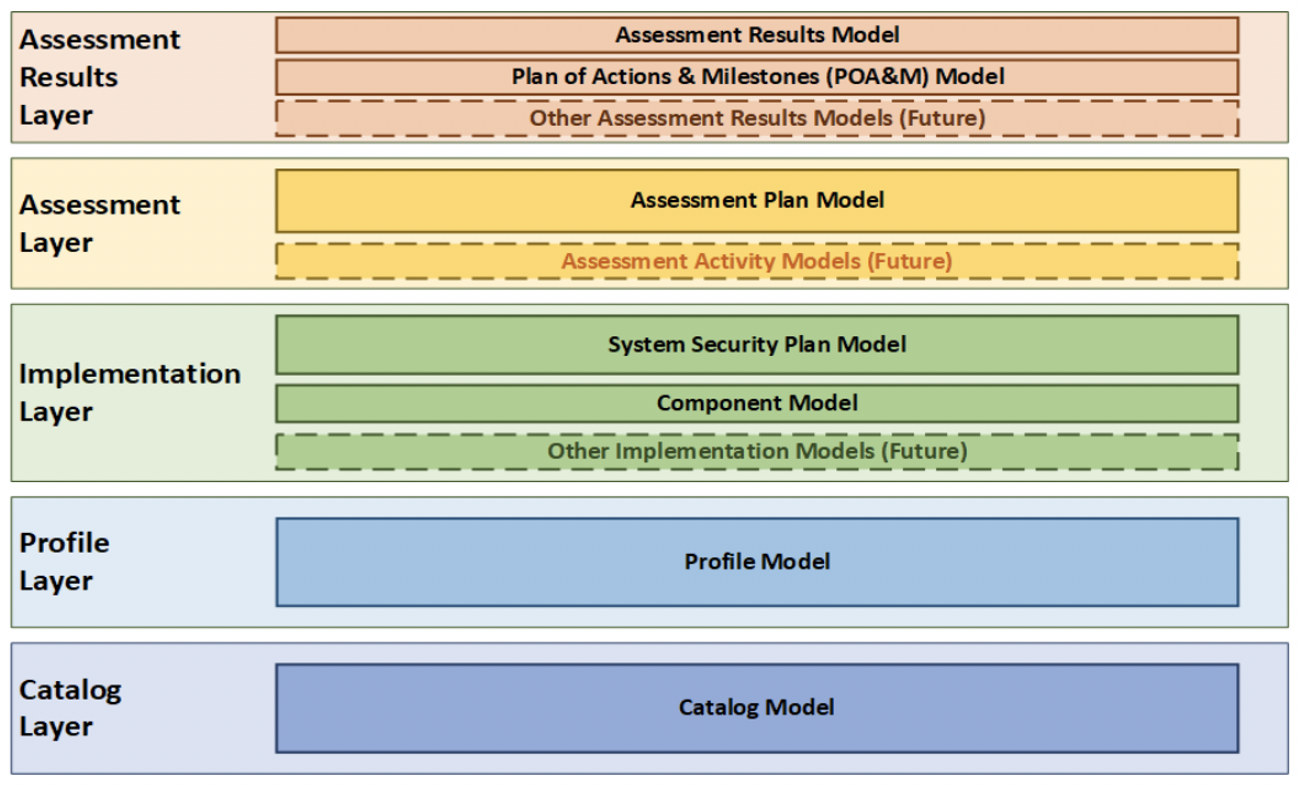
The Geek or tool developer will utilize OSCAL’s ‘Layer and Model Reference’. The architecture is made up of a series of Layers. The series of Layers will provide a set of Models.
- Catalog Layer – structures a collection of controls in catalog that are represented in a structure, machine readable format.
- Profile Layer – provisions for a model that selects a specific set of control requirements from one or more catalogs.
- Implementation Layer – describes how controls are implemented, as in a specific system or a distributed component that then incorporate into a system.
- Assessment Layer – description of the assessment plan information.
- Assessment Results Layer – capturing the assessment’s results and findings.
The Cybersecurity End All
We looked at the C Level Executive and the Geek (developer) perspectives. Advantages for both parties assist them in managing multiple regulatory frameworks. Conclusively, OSCAL is simplifying the risk management of many security plans and mapping the different frameworks into a single security plan.
Looking to future use of OSCAL, other efficiency methods can be integrated within OSCAL, enabling it to support other company roles and efforts. One such efficiency method that can be integrated into OSCAL for this purpose is RegAudit. As a tool that assists in compliance of regulatory controls, OSCAL eases the pain of handling multiple regulatory controls. RegAudit remaps the regulatory controls for ease of interviewing. RegAudit supports the IT functionality relationships where mapping within OSCAL’s Catalog layer occurs for the regulatory controls. This and other processes help to automate Cybersecurity assessments and security plans.
The question is “Can your company take advantage of OSCAL?” Don’t let Cybersecurity Frameworks complicate your intricate IT environment and assessments. Be bold and reach out to simplify your compliance.
Robert Ashcraft, CEO of CMMC Solutions
Robert.Ashcraft@cmmc-solutions.com
Special thanks to NIST for their support to our Cybersecurity frameworks and support of this article. A special welcome to Dr. Michaela Iorga for her support and assistance on our understanding OSCAL. Note that the OSCAL information as referenced in this article was obtained from the NIST – OSCAL website: https://pages.nist.gov/OSCAL/
This article was featured in the 2020 PSC Annual Conference Thought Leadership Compendium. See the full PDF version here.